Fraud Moves Fast. Your Controls Need to Move Faster.
At Cook Solutions Group, we've been part of the financial community from the start. Most of what we build came from sitting alongside fraud professionals exactly like you — listening to the problems that kept you up at night and engineering solutions with what we like to call the CSG Twist: practical, integrated, and built for the real world.
This guide is drawn directly from that experience. Fraud is no longer a slow-moving threat. From AI deepfake voice cloning to jackpotting attacks on self-service terminals, the pace of risk has fundamentally shifted. Traditional controls — siloed vendors, manual logs, reactive alarm systems — are struggling to keep up.
"The goal isn't more tools. It's the right controls, working together every day — giving you visibility, accountability, and the confidence that comes from being genuinely prepared."
What follows is a breakdown of the six most pressing fraud threats facing banks and credit unions today — with early warning signs to watch for and proven strategies to address each one.
Common Fraud Threats Facing Financial Institutions Today
Each section below breaks down how these risks surface — and the practical controls that stop them.
ATM & ITM Fraud
Skimming devices, physical tampering, malware, and organized cash harvesting attacks targeting your self-service fleet.
Check & Deposit Fraud
Counterfeit, altered, and stolen checks moving through teller lines, ATMs, and remote deposit channels faster than manual review.
Account Takeover & Social Engineering
Phishing, vishing, AI voice cloning, and stolen credentials used to impersonate customers and pressure staff past procedures.
Insider Risk & Cash Discrepancies
Weak dual controls, manual logs, and gaps in video coverage that create opportunity for internal actors.
Alarm Fatigue & Missed Incidents
Excessive false alarms overwhelm teams — slowing response and masking genuine threats in the noise.
Compliance Gaps & Audit Burden
Fragmented vendor relationships, incomplete records, and inconsistent logs that make audits stressful and time-consuming.
ATM & ITM Fraud
Self-service terminals continue to be prime targets. Skimming devices, physical tampering, malware installs, and organized jackpotting operations can drain machines and compromise customer data — often before anyone notices something is wrong.
⚠ Early Warning Signs
- Bezel misalignment or missing decals
- Unfamiliar or unknown hardware attached
- Adhesive residue or drilled/scratched panels
- Irregular or unexpected card reader activity
- Unexpected device errors at the terminal
- Cabinet access logged after hours
🛡 How Institutions Stop It
- Physical ATM/ITM hardening to deter and delay attacks
- Real-time tamper alerts and suspicious activity notifications
- Fraud Detection Engine flagging abnormal transactions automatically
- 24/7 remote monitoring — experts watch, so your team isn’t stuck reacting
The CSG Twist: We combine intelligent analytics with human-verified monitoring, so alerts that reach your team are real — not noise.
Check & Deposit Fraud
Counterfeit and altered checks now move through teller lines, ATMs, and mobile deposit channels faster than manual review processes can keep up with.
⚠ Early Warning Signs
- Repeat offenders conducting suspicious transactions
- Unusual transaction times or dollar amounts
- New accounts receiving immediate high-dollar deposits
- Altered checks — different ink color or pen thickness
- Deposits followed immediately by withdrawal attempts
- Deposits from IP addresses or devices with fraud history
🛡 How Institutions Stop It
- Cloud-native check imaging platforms with automated workflows
- Serverless architecture that reduces infrastructure risk
- Industry-leading validation datasets for real-time verification
The CSG Twist: Cloud-native imaging + automation reduces operational friction while tightening fraud controls.
Account Takeover & Social Engineering
Attackers use phishing, vishing, and AI voice cloning to impersonate customers or staff. Once inside, they pressure employees to bypass steps — and speed is the advantage they count on.
⚠ Early Warning Signs
- Unusual access times inconsistent with typical behavior
- Repeated failed login attempts signaling credential testing
- Exceptions to established security policies
- Requests that deviate from standard workflows
🛡 How Institutions Stop It
- Named credentials with defined schedules and audit trails
- Unified access control linking physical + logical events
- Video analytics tied to access events for visual verification
- Cloud access control for real-time visibility across locations
The CSG Twist: When access events link to video, exceptions become verifiable facts — not assumptions.
Insider Risk & Cash Handling Discrepancies
Insider risk grows when dual control is weak, logs are manual, and video evidence isn’t integrated. The fix is centralized accountability — so activity is visible and traceable end to end.
⚠ Early Warning Signs
- Unscheduled vault or secure-area access
- Unexplained end-of-day adjustments
- Missing or inaccessible surveillance footage
- Records that don’t align across systems
🛡 How Institutions Stop It
- Managed access control for vaults with full logging
- Professionally installed safes and vault systems
- Centralized case management linking access, video, and reports
- Streamlined investigations with unified evidence
The CSG Twist: A closed-loop system makes concealment structurally harder — because every step leaves a trail.
Alarm Fatigue & Missed Incidents
Too many false alarms overwhelms teams, slows response, and increases the odds real incidents go unseen. This is where “less noise” becomes a security feature.
⚠ Early Warning Signs
- Repeated nuisance alerts from the same zones
- Frequent alarm cancellations
- Slow dispatch times becoming routine
- After-hours events receiving no verification
🛡 How Institutions Stop It
- Managed services that prioritize and consolidate alarms
- 24/7 monitored video verification to reduce false dispatches
- Single command environment for incident + health oversight
The CSG Twist: Human-verified alarms = fewer false dispatches and faster action when it’s real.
Compliance Gaps & Audit Readiness
Fragmented vendor relationships create fragmented records — and that makes audits painful. Audit readiness becomes much easier when your evidence, maintenance history, and logs live in one place.
⚠ Early Warning Signs
- Missing or incomplete maintenance histories
- Logs that don’t reconcile across systems
- Delays exporting evidence when needed
- Device records that are incomplete or hard to track
🛡 How Institutions Stop It
- Unified device tracking, tickets, and reports in one platform
- Monitored network backbone for ongoing visibility
- Complete historical records available on demand
- Vendor consolidation to reduce fragmentation and risk
The CSG Twist: One source of truth turns audit prep from a fire drill into a routine report.
A Comprehensive Fraud Prevention Checklist
Validate your program against these proven controls — and quickly spot the gaps.
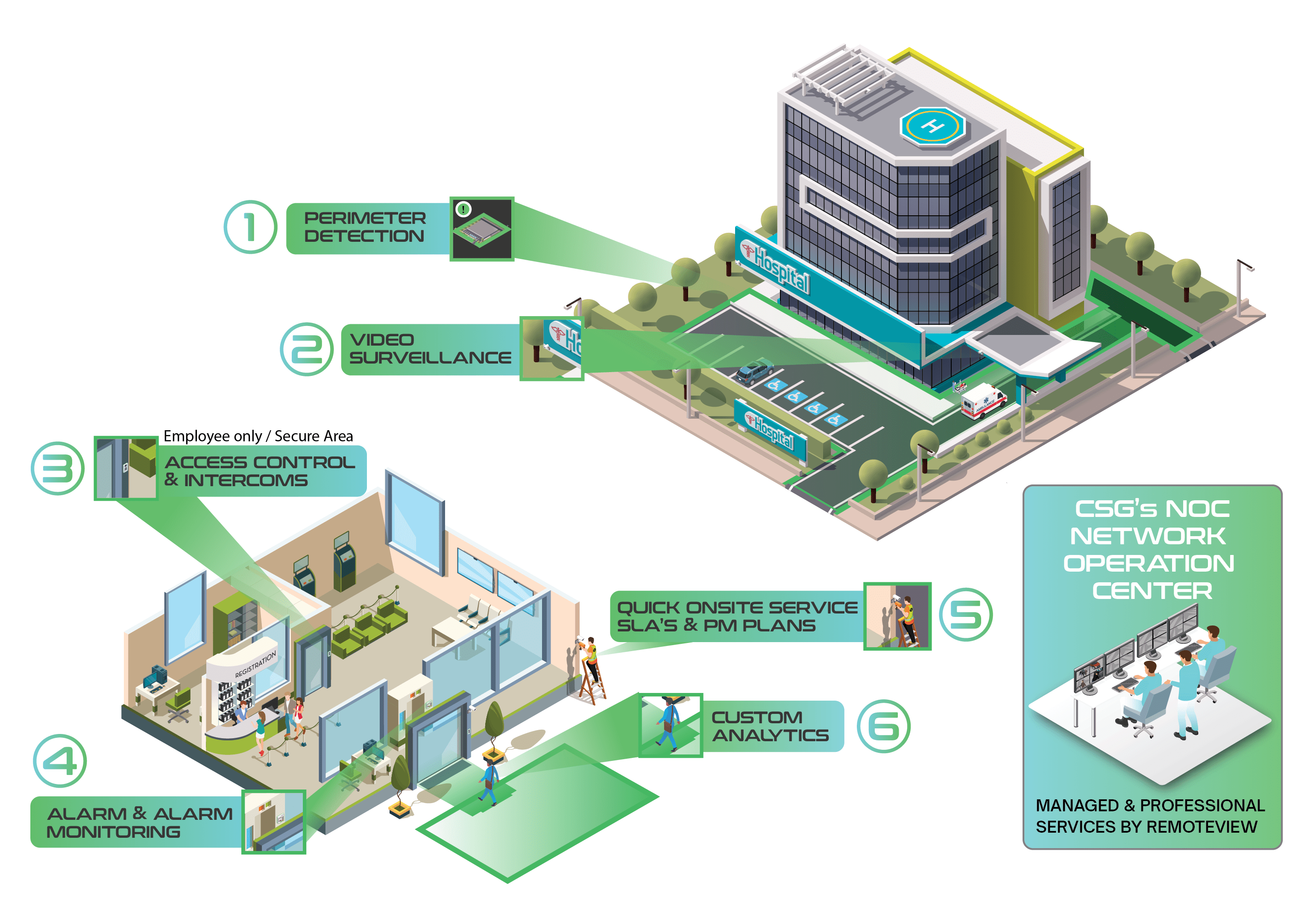
Open Video System Integration
Integrate VMS with access, alarms, and transaction data. Add managed services for 90-day retention, patching, and human-verified confirmation.
Advanced Analytics
Line crossing, object detection, and custom rules that surface threats without manual review.
Suspicious Activity Notifications
Detect loitering or unauthorized device installs at machines with proactive alerts.
Fraud Detection Engine
Continuous monitoring with the ability to proactively disable machine access when fraud is suspected.
Centralized Case Management
One dashboard for investigations and evidence—always ready for law enforcement requests.
Vendor Due Diligence
Reduce fragmented vendor relationships to improve integrations, efficiency, and risk posture.
Cloud-Based Check Imaging
Cloud-native architecture + automated workflows and strong validation data to reduce check fraud exposure.
Equipment Health Transparency
Centralize tickets, service requests, reporting, and device status—no blind spots.
Event-to-Video Access
Instantly pull video tied to an alarm, access event, or incident for faster investigations.
Hard Drive Encryption
Protect sensitive data using the highest available encryption standards.
Managed Cloud Access Control + Video Verification
Reduce false dispatches and improve protection with 24/7 verification and remote management.
Risk Assessments & Security Consulting
Validate your program against standards, identify gaps, and strengthen your risk-based strategy.

Fraud Guide
Request the Fraud Guide for Banking Security Professionals
Get practical warning signs, a layered defense framework, and a checklist you can use to reduce loss, improve visibility, and simplify audit readiness.
Want the “CSG Twist”? Ask us how to unify video, access, alarms, and case evidence.





































.png)







